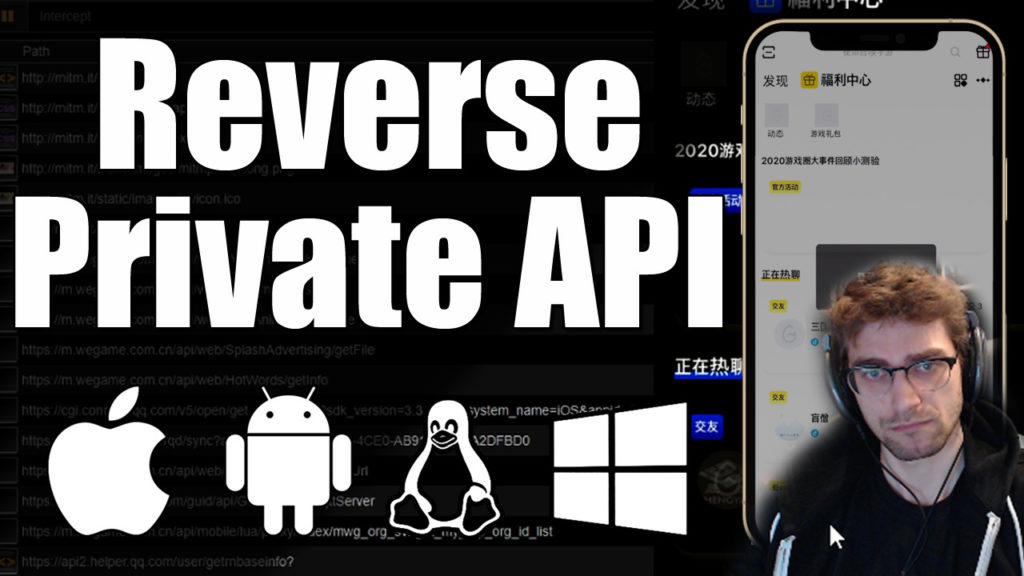
Have you ever wanted to access data from an application that doesn't provide a Public API? Well I've got great news. That application is getting its data from somewhere. You just need to find out how to plug into it! This process is called Reverse Engineering (Or hacking if you want to pretend you're really smart) a Private API. I will document some tips and useful tools that will help you reverse any Private API from any application on any platform.
Tools
There are a handful of tools that can be used to complete this task. Windows 10 was my platform of choice for working with the data so I'll be sharing what I used on here.
Fiddler: Fiddler is an HTTP/HTTPS Proxy that can be used to intercept and decrypt SSL/HTTPS traffic. This application is also useful for replaying requests, creating custom request, and exporting a request as cURL to be converted into Python 3. Fiddler is free to use, just sign in with your Google Account! Make sure you install the certificate and enable HTTPS mode so you don't miss any requests. https://www.telerik.com/fiddler
MitM Proxy: Man in the Middle Proxy is a great way to read data from Smart Phone Applications. This is what I used to get all the data I needed for my API reversal. Simply download the executable from https://mitmproxy.org/ to start up a server (disable your firewall or open port 8080) and then enter your PC's IP address into the Proxy Server settings of your Phones WiFi settings. After that navigate to http://mitm.it/ on your Phone and install the provided certificate. Follow the provided instructions on http://mitm.it/ and start sniffing!
Tips
Create a text document to save all your finding and especially any useful URL endpoints you find. Having your information organized will help to ensure that you don't waste time on the same thing twice or need to proxy your device over and over again to find what a request should look like.
For more information and an example of the API reversed you can watch my YouTube tutorial here.
